Digital growth raises your exposure to cyber, operational, and reputational threats – fast. Hence, the digital risk management (DRM) market is expected to keep growing, from an estimated 13.32 billion in 2025 to 24.02 billion by 2029 (CAGR of 12%.). Leaders who treat risk as a core business capability, not a compliance task, outperform peers in resilience, speed, and trust. In this guide, we show you how to connect DRM with talent strategy to prevent incidents, reduce impact, and sustain growth.
Why digital risk management is a C-suite imperative
The stakes for digital security have never been higher. Your organization’s value depends on how well you protect data, systems, customers, and your brand. That makes digital risk management a leadership responsibility, not just an IT function.
The financial impact is equally sobering, with an average global data breach cost of $4.88 million during 2024. And according to PwC Global Digital Trust Insights, 60 percent of companies plan to increase their cyber risk budgets in 2026.
For the C-suite of any company, these are the main reasons to create a digital risk management strategy:
- It protects revenue and reputation. A single disruption can trigger lost sales, regulatory scrutiny, and customer churn. Strong digital risk protection reduces both frequency and blast radius.
- It improves decision velocity. An explicit IT governance framework clarifies who decides what, when, and how – so risk reviews accelerate, not stall, delivery.
- It aligns investment to exposure. Treating IT risk management as portfolio management helps you fund controls where risk concentration is highest (critical systems, sensitive data, third parties).
- It clarifies CISO responsibilities. Your CISO should own the enterprise security strategy, risk posture reporting, control standards, and incident response playbooks, and work hand in hand with every department.
- It embeds trust by design. A living data governance policy defines data ownership, quality, lineage, access, and retention, so privacy and compliance are built into daily work.
The unseen link: The cybersecurity talent gap and digital threats
The harsh reality for companies is that they can buy tools, but they cannot outsource accountability. ISC2's 2024 Cybersecurity Workforce Study revealed a critical global gap of 4.8 million unfilled positions, and the nature of the cybersecurity talent gap has evolved. According to the same study, 33 percent of organizations cite lack of budget as the primary cause of talent shortages – surpassing the traditional challenge of finding qualified candidates.
This shortage directly widens your exposure. Talent gap in security engineering, cloud security, identity management, and data protection slows remediation, increases misconfigurations, and stretches on-call coverage thin. At the same time, the challenge intensifies when you factor in third-party risk management. You now inherit risk from SaaS providers, managed service providers, and data partners. Vendor engineers become an extension of your attack surface and change-management discipline.
The consequences manifest as reputational risk examples that multiply by the day. A misconfigured storage bucket, an unvetted marketing tool, or a breached vendor can trend on social media in minutes and erode stakeholder trust. This is why talent risk management matters as much as any technical control and makes succession planning strategy essential for long-term goals.
Building a resilient digital risk strategy framework
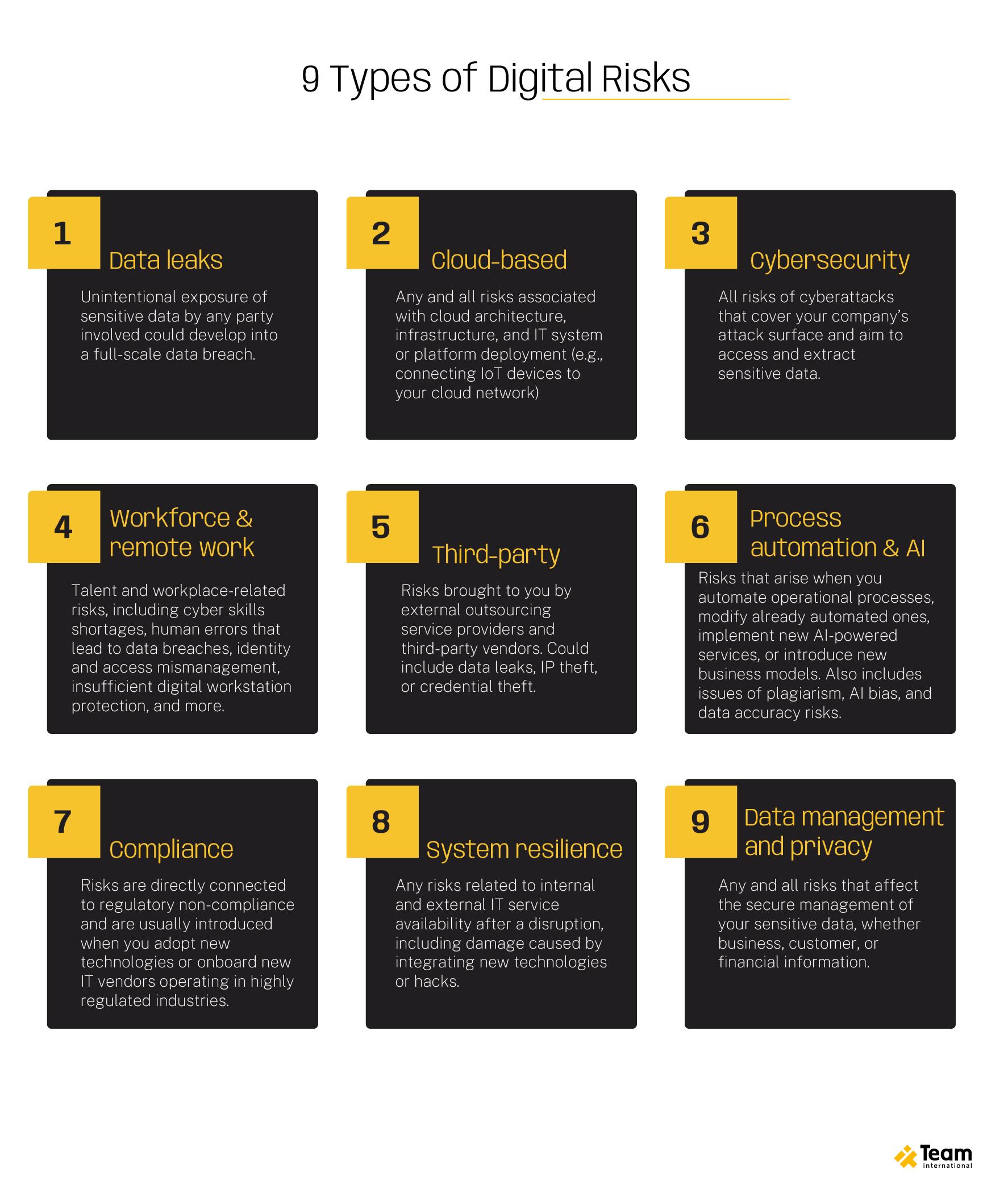
A resilient digital risk strategy starts by understanding what you're protecting and why. The nine types of digital risks don't exist in isolation. One can trigger another one and so on. Managing these interconnected threats requires a systematic framework that balances proactive prevention with rapid response, and the CISO's role has evolved to orchestrate this entire strategy.
Here's how to build one:
1. Set risk appetite and objectives
Start by defining what "good" looks like for your organization. Establish acceptable downtime thresholds, data sensitivity tiers, recovery time objectives, and tolerance levels for third-party dependencies. Then tie these risk objectives directly to business KPIs so leadership can make informed trade-offs between speed and security.
2. Map your digital estate and crown jewels
You can't protect what you don't know exists. Inventory assets across applications and prioritize your "crown jewels" – the systems and data that would materially impact revenue, safety, or reputation if compromised.
3. Identify and assess digital transformation risks
As you modernize, watch for common risk patterns and build third-party risk management into procurement and onboarding from day one, not as an afterthought. Every vendor relationship extends your attack surface and inherits your accountability.
4. Test readiness and measure performance
Untested plans are meant to fail. Run tabletop exercises, red-team scenarios, and recovery drills regularly. Track both leading indicators and lagging indicators (time to detect, time to respond, breach frequency). This data tells you where your framework is strong and where gaps persist.
5. Close the loop with data governance
Finally, operationalize your data governance policy by defining clear stewardship roles, establishing data catalogs, conducting regular access reviews, and tracking lineage. Strong data governance is the control that prevents your other investments from being undermined by rogue data sets or abandoned projects.
Strategic talent management to mitigate digital risks
Upskilling cybersecurity and mitigating the talent gap requires strategic workforce planning that goes beyond traditional recruiting. Organizations must adopt a multi-faceted approach: developing internal talent, diversifying hiring pipelines, and creating retention-focused cultures.
Succession planning strategy takes on new urgency in cybersecurity contexts. With demand far exceeding supply, organizations cannot rely solely on external hiring. Instead, implement structured career pathways that enable IT professionals to transition into security roles. The ISC2 study showed that while IT remains the primary pathway with 70 percent of cybersecurity professionals, 18 percent entered from non-IT positions.
Retention strategies matter as much as recruitment. Create environments where cybersecurity professionals can grow, innovate, and maintain work-life balance. Consider job rotation to prevent burnout in high-stress roles like security operations. Recognize that losing a trained professional doesn't just create a vacancy – it eliminates institutional knowledge about your specific systems and threat landscape.
For organizations unable to maintain full in-house teams, strategic partnerships with managed security service providers offer an alternative. This approach provides access to specialized expertise while allowing internal teams to focus on strategic initiatives rather than 24/7 monitoring. The key is ensuring third-party providers integrate seamlessly with your broader digital risk management framework.
Future-proofing your organization: Integrating risk and talent
The future of organizational resilience lies in recognizing that managing digital risk protection and talent strategy are inseparable. Organizations that excel in both dimensions share common characteristics: they view cybersecurity as a business enabler, not a cost center; they invest in people as much as technology; and they foster cultures where risk awareness permeates every function.
The path forward requires balanced investment: advanced security technologies paired with robust talent development; proactive risk assessment combined with succession planning; and IT governance frameworks supported by risk-aware cultures. Organizations that master this balance will turn security capabilities into competitive advantages.
If you are ready to operationalize a modern digital risk management – and build the talent engine to sustain it – let’s talk. With 20+ years of experience in delivering IT advisory, security engineering, and managed services, we can help you integrate risk and talent into a resilient operating model, accelerate time-to-value, and protect what matters most to you.
